Setting up Security Analytics
Before Security Analytics can begin generating findings and sending alerts, administrators must create detectors and make log data available to the system. Once detectors are able to generate findings, you can fine-tune your alerts to focus on specific areas of interest. The following steps outline the basic workflow for setting up components in Security Analytics.
- Create threat detectors and alerts, and ingest log data. See Creating detectors for more information.
- Consider creating correlation rules to identify connections between events and possible threats occurring in different logs throughout your system.
- Inspect findings generated from detector output and create any additional alerts.
- If desired, create custom rules to better focus detectors on high-priority concerns in your system. See Creating detection rules for more information.
Navigate to Security Analytics
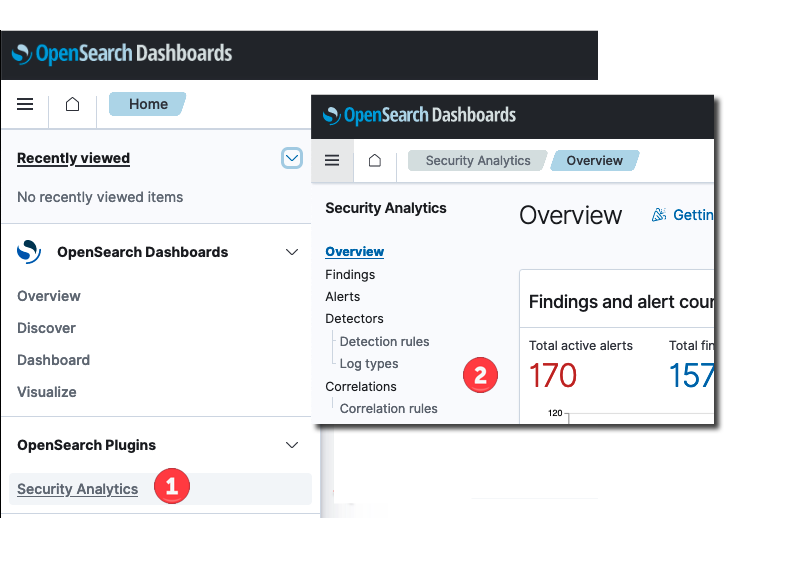
- To get started, select the top menu on the Dashboards home page and then select Security Analytics. The Overview page for Security Analytics is displayed.
- From the options on the left side of the page, select Detectors to begin creating a detector.